Firewall (computing)
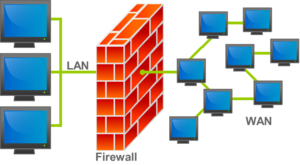
A firewall is a system which filters network activity and permits presumably safe internet/intranet traffic while blocking suspicious or unwanted communication.[1] There are several types of firewall and methods of filtering.
Contents
Physical and Virtual
Firewalls can be either physical devices which sit on the network between the Internet and the internal client, or software systems which are installed onto the client's device.
Hardware
Hardware firewalls are generally considered the best front-line of defense. When an incoming connection reaches the protected network, the connection must first go through this hardware firewall. If the connection is unwanted, it will generally be ignored. In this case, the entity attempting to connect will simply have their request time out. Some firewalls will outright reject the request, however, which is a less effective defense method. (If rejected outright, a potential attacker will know he has found an active device, whereas if the request is ignored, it will be more difficult to know if there is even a device to connect to.)
To the outside world, there is only one device (the firewall) on the protected network. Even when a connection is permitted, the communication still passes through the firewall using a specified port. Therefore, even active connections do not reveal the internal IP address of devices.[2]
However, many hardware firewalls (all but the newest types) often do not know what connections are being used for. Most do not collect the packets and reassemble messages, so connections can be abused without the firewall knowing. Even the ones which do attempt to analyze traffic can have difficulty understanding what is going on.[2]
Some firewall configurations also offer what is called a "DMZ." This is a separate section of the network which is protected from the outside, but also cannot communicate directly with the inside network—it must go through another firewall (or the same one again) first. Sometimes certain servers and honeypots are placed here.
Software
Software firewalls are not typically considered a good first line of defense, but a good addition to a tiered defense system. They digitally intercept and attempt to analyze traffic on the client's system. Since this kind of firewall operates on the OSI model's application layer, it has an easier time of understanding what the communication link is being used for. Additionally, this host firewall filters traffic within the local area network, meaning that unwanted traffic from other hosts behind the perimeter firewall can still be blocked.[3]
Host firewalls rely on the operating system in order to operate properly. This means that if the host system is infected or otherwise compromised, the software firewall can be prevented from blocking unwanted traffic.[2]
Types
There are a number of different types of firewall. Each type attempts to protect a network using different methods.
Proxy firewall
Less for defense than for utility, the proxy firewall simply redirects certain kinds of traffic to a proxy, while letting other traffic pass directly through. Alternatively, it can be used to redirect all traffic non-selectively to the proxy, if desired. This is not a type of firewall which is commonly used in modern networks, although this feature can be used in conjunction with others in a more advanced firewall system.[4]
Stateless inspection
A stateless firewall has the ability to analyze traffic and permit passage based on static values, such as the source IP address and the destination. All filtering is done by static rule sets. There are no automated processes to determine what has been requested or make any other sort of conclusion.[5]
Stateful inspection
Stateful firewalls are now considered the norm for network security. They monitor the state, port, and protocol used in all communication. They then make decisions based on context, or previous observations, as well as any rules the administrator has set.
Unified threat management
These firewalls use stateful inspection, but also offer some additional functionality. They incorporate some variety of intrusion prevention system to help prevent network penetration by attackers. They also include an antivirus solution to help keep malware out of the network.[4] Depending on the UTM system, spam blocking, suspicious file sandboxing, data loss prevention, and many other features can be built into it.[6] Additionally, they generally offer customizable, interactive reports so that administrators can easily monitor and understand activity.[7]
Next-generation
As one of the newest kinds of firewall, this type offers all of the basic protections listed above, but also has a better view into the application layer. It is capable of understanding what software is operating over the network, and detecting more sophisticated threats. Intrusion detection is also more advanced in this type of firewall.[4]
Threat-focused NGFW
As the name suggests, this type of next-generation firewall is even more focused on threat detection and remediation than its predecessors. It has better context awareness and evasion detection than any of the earlier types, and includes automated responses to penetration attempts and other unwanted communication.[4]
Prevalence
Almost every modern computer is protected by some kind of firewall, at some point along the connection link. Most network address translation (NAT) routers, include some form of firewall as well; even if not designed with a firewall, NAT routers can be barriers to some basic methods of attack due to the core functions of the device. The majority of networks in operation today do use NAT routers, meaning that most people are protected in this fashion.
Additionally, many anti-virus programs now come with a software firewall. However, even more common than this are firewalls native to the operating system. Windows Firewall, for example, is a preinstalled firewall system in all modern versions of the operating system.
This kind of popular protection is far better than nothing, but to ensure a network or device is secure, firewalls should not be as much of an add-on or an after-thought as a deliberate security measure. When attacking a Windows device, the attacker knows for certain that they will need to circumvent the native firewall—therefore part of the standard attack planning includes a method to get around or through that firewall. Some people say that windows firewall is a very good product,[8] while others argue that it is too trusting.[9] For this reason, third-party firewalls such as the ones which sometimes come with anti-virus software are favored. For those more concerned with securing their network, a separate hardware firewall may be desired as well. Those who do not use such a device would be well advised to ensure that their NAT router's firewall firmware is up to date.
References
- ↑ “Definition of firewall in English by Oxford Dictionaries.” Oxford Dictionaries | English, Oxford Dictionaries, http://en.oxforddictionaries.com/definition/firewall. Accessed 6 Sept. 2017.
- ↑ 2.0 2.1 2.2 “What is a Firewall?” WhatIsMyIPAddress.com, http://whatismyipaddress.com/firewall. Accessed 7 Sept. 2017.
- ↑ “Firewall Types.” TechNet, Microsoft, http://technet.microsoft.com/en-us/library/ff602917(v=ws.10).aspx. Accessed 7 Sept. 2017.
- ↑ 4.0 4.1 4.2 4.3 “What Is a Firewall?” Cisco, 6 Sept. 2017, http://www.cisco.com/c/en/us/products/security/firewalls/what-is-a-firewall.html. Accessed 7 Sept. 2017.
- ↑ “Stateful vs. Stateless Firewalls.” InetDaemon, http://www.inetdaemon.com/tutorials/information_security/devices/firewalls/stateful_vs_stateless_firewalls.shtml. Accessed 8 Sept. 2017.
- ↑ “Unified Threat Management.” WatchGuard Technologies, 25 Aug. 2017, http://www.watchguard.com/wgrd-solutions/unified-threat-management. Accessed 7 Sept. 2017.
- ↑ “Unified Threat Management | Cloud Security & Data Loss Prevention.” MegaPath, http://www.megapath.com/security/unified-threat-management/. Accessed 7 Sept. 2017.
- ↑ “ Windows 7 Firewall- Is it good enough? .” Microsoft Community, Microsoft, http://answers.microsoft.com/en-us/windows/forum/windows_7-networking/windows-7-firewall-is-it-good-enough/cc1c218a-0162-4b69-a9a9-194069d55ace. Accessed 8 Sept. 2017.
- ↑ “Is Windows Firewall Any Good??” Windows Legacy OS forum, CNET, https://www.cnet.com/forums/discussions/is-windows-firewall-any-good-204842. Accessed 8 Sept. 2017.